How To Use AI To Help Keep Your Financial Data Safe
KEY TAKEAWAYS
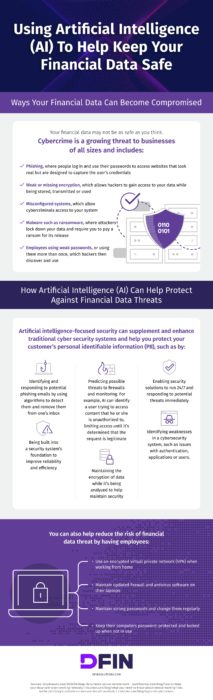
Cybercrime is on the rise. In fact, recent research shows a 600% increase in global cybercrime since the beginning of the pandemic. With remote and hybrid work here to stay, there’s a growing opportunity for cybercriminals to take advantage of disparate and disconnected systems to compromise key data.
While any breach is worrisome, certain types of information — such as financial data related to transactions, payroll, or purchases — pose significantly more risk to corporate reputation and revenue. Best case scenario: Issues are caught early and damage is minimal. Worst case: Attackers steal and sell data online, while companies are on the hook for monetary losses and reduced customer trust.
It’s not all bad news: Advancements in artificial intelligence tools can help safeguard your financial data. Here’s how.
How Hackers Attack
Malicious actors aren’t picky about how they access systems. Put simply, if they see an opening, they’ll take it. The recent shift to remote work offers an abundance of opportunities.
Common attack vectors include:
- Phishing: Phishing attacks see hackers sending fraudulent emails that encourage staff to open malicious links or download infected files, which, in turn, collect employee login and password details. Attackers then leverage these credentials to gain network access.
- Weak encryption: Encryption forms the front line of data defense. By obfuscating information sources with strong encryption, attackers gain no value from theft or access. The problem is, many companies leverage easily compromised encryption protocols or skip this security step.
- Ransomware: Ransomware remains one of the most prevalent cybersecurity threats worldwide — because it works. If attackers gain access to business networks and encrypt key data, they can often compel companies to pay for their release.
What Employees Can Do
To help mitigate the impact of potential attacks, businesses can ask employees to take simple steps, such as:
- Connecting via VPNs: When working from home or on the road, employees should use virtual private networks (VPNs) to connect with company servers. These VPNs not only obscure user locations, but provide an encrypted tunnel for data in both directions.
- Regularly changing passwords: Weak passwords remain a problem. Simple combinations such as 123456 regularly make the list of the most common passwords every year. As a result, it’s critical for employees to regularly change their passwords and ensure they contain letters, numbers and even special characters to reduce compromise risk.
Where AI Can Help
Despite best efforts around awareness and education, attackers are becoming more adept at circumventing common protection. It makes sense: Hackers have the benefit of trying multiple techniques against multiple targets to see what sticks, while organizations are forced to respond as attacks occur.
Artificial intelligence tools trained with machine learning (ML) algorithms can detect and predict potential security problems. As a result, AI-focused security can help level the playing field by:
- Identifying potential hooks: AI phishing tools can quickly scan emails and identify common characteristics associated with phishing attacks. These emails are then removed from user inboxes before they’re ever seen or clicked — and can also be stored for later analysis by IT security teams.
- Predicting possible threats: Knowing what’s coming can help limit the impact. Trained AI tools can pinpoint potential risks as they occur. For example, if AI tools detect odd requests from users based on behavioral details such as time of login, location or the type of data access being requested, these tools can suspend access requests until teams have confirmed their legitimacy.
- Enabling 24/7/365 protection: AI tools work best in concert with human oversight, but offer the benefit of never having to take breaks. Leveraging intelligent security solutions makes it possible for companies to gain 24/7/365 protection that’s always ready to respond.
As a cybersecurity professional, want to learn more about the evolving landscape of financial data protection? Dive into our defensive resource.





